
Blog
Mitigating cyber risk: A new approach in the digital age
As technology evolves, so does the network of bad actors who take advantage of it for illicit gains, leaving governments scrambling to modernize the way they regulate criminal activity. Therefore, governments and regulators find themselves engaged in a digital war against bad actors to regulate and monitor rapidly changing trends and technologies.
This article discusses the changing landscape of cybercrime and the challenge of cyber risk in an era of exponential risk and shares a new mindset for managing risk, through a growing body of knowledge, data, and powerful analytical tools.
In the wake of the digital revolution, the global landscape has witnessed an unprecedented surge in cybercrime, reshaping the paradigms of security and risk management. Since 2016, malicious cyber activities have surged, propelled by the increasing sophistication of cybercriminals and the rapid expansion of digital infrastructure.
Let's delve into the multifaceted dimensions of cybercrimes, and review the trends, challenges, and implications that have characterized this transformative era.
The escalating threat landscape
ECrime – criminal activities that involve computers or the internet – was deemed the most persuasive threat across the 2023 cyber landscape according to the 2024 Global Threat Report by cybersecurity firm CrowdStrike. Other 2023 themes included identity based threats, social engineering, and exploitation of third-party relationships. The report also highlighted emerging risks like generative AI (artificial intelligence), which could lower the barrier for entry to cybercrime.
The escalation in malicious cyber activities underscores the pressing need for robust cybersecurity measures and proactive risk mitigation strategies. Cybersecurity Ventures, a leading researcher and publisher covering the global cyber economy, estimates cybercrime costs will grow by 15% annually over the next 5 years, and reaching $10.5 trillion by 2025.
The evolution of cyber-enabled crimes
The advent of the digital age catalyzed a wholesale shift in criminal activities, with traditional offenses being redefined and amplified through the use of information communication technology (ICT).
Cyber-enabled crimes, encompassing a spectrum of illicit activities ranging from harassment to extortion, have proliferated in both frequency and severity. Unlike cyber-dependent crimes or fraud, these offenses can transpire even in the absence of ICT but are exponentially magnified when technology is involved. This convergence of traditional crimes with digital platforms has blurred the boundaries of physical and virtual worlds, presenting a myriad of challenges for law enforcement agencies and regulatory bodies.
The pervasive nature of cybercrimes poses an existential threat to the security and integrity of individuals, organizations, and economies worldwide. By infiltrating and illicitly acquiring sensitive assets such as financial resources, intellectual property, and personally identifiable information (PII), cybercriminals undermine individual privacy and the economic stability of entire sectors and nations.
The ripple effects of cyberattacks reverberate across all sectors, ranging from banking and finance to healthcare and critical infrastructure, amplifying the magnitude of their impact. Moreover, the rise of ransomware attacks and data breaches has engendered a climate of fear and mistrust, eroding public confidence in digital ecosystems and impeding socio-economic progress.
Cybercriminals, as highlighted by the Federal Bureau of Investigation (FBI), exploit vulnerabilities in US networks, perpetrating theft of financial and intellectual property while jeopardizing critical infrastructure with impunity.
The United Kingdom National Health Service Counter Fraud Authority defines cyber fraud as financially motivated cybercrime, resulting in fraudulent activities. And the healthcare industry remains a prime target due to the lucrative nature of medical data on the dark web.
The Federal Trade Commission reports a staggering $8 billion lost to fraud in 2022, with identity theft constituting a significant portion of over one million reported cases.
Common cybercrimes include business email compromise (BEC), identity theft, spoofing and phishing, online predation, elder fraud, romance scams, and ransomware attacks, each posing unique threats to individuals and organizations alike.
The cost of cyberattacks is staggering, with data breaches reaching unprecedented levels of financial impact.
- According to IBM's Cost of a Data Breach report, 2023 saw a global average breach cost of $4.45 million, with US-based companies facing costs exceeding $10 million.
- Deloitte highlights the exacerbated risks in the post-pandemic landscape, with increased use of personal devices for business purposes and vulnerabilities in remote work setups.
- The ACAMS 2022 Global Ransomware Risks Survey reveals a growing threat perception, with 65% of respondents viewing ransomware as a significant concern.
Cybercriminals are evolving their tactics, leveraging ransomware-as-a-service (RaaS) and targeting software supply chains to maximize victim count. As defenders become more adept, attackers innovate, reducing the average completion time of ransomware attacks and increasingly using backdoor access to disrupt systems. Case studies underscore the real-world impact of these cyber threats on businesses, highlighting the urgent need for comprehensive cybersecurity measures.
Observations from Moody’s intelligent screening database
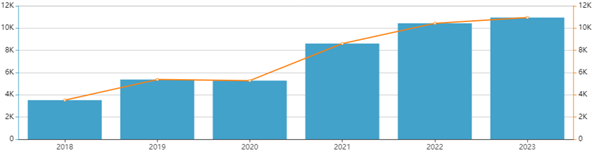
Moody’s screening database highlights this increase by the number of profiles added annually for cybercrimes including cyberstalking, hacking, phishing, internet swindles, and cybercurrency related crimes. The volume of profiles in our database with cyber-related risk have nearly doubled since 2020.
The cyber regulatory landscape
In response to the escalating threat posed by cybercrimes, governments and regulatory bodies worldwide have intensified efforts to bolster cybersecurity frameworks and enact stringent regulations. The global cyber regulatory landscape is characterized by a diverse range of policies, directives, and standards aimed at mitigating cyber risks and promoting resilience across industries.
In the European Union, the General Data Protection Regulation (GDPR) sets out comprehensive data protection measures, mandating stringent requirements for the handling and processing of personal data.
Similarly, the Cybersecurity Law in China imposes strict cybersecurity obligations on network operators and mandates the protection of critical information infrastructure.
In the United States, regulatory initiatives such as the Cybersecurity Enhancement Act and the Cybersecurity Information Sharing Act seek to enhance information sharing and collaboration among public and private sector entities to combat cyber threats.
Despite these regulatory efforts, the global cyber landscape remains fragmented, with varying levels of compliance and enforcement across jurisdictions. The lack of harmonization and interoperability between regulatory frameworks poses challenges for multinational corporations operating in multiple jurisdictions, which necessitates a nuanced approach to regulatory compliance and risk management.
A new approach to mitigating cyber risk
In the face of escalating cyber threats, traditional risk mitigation strategies are proving inadequate to safeguard against the dynamic nature of cybercrimes. Recognizing the need for a new approach, organizations are turning to innovative solutions such as cyber risk ratings and analytics from Bitsight to manage cybersecurity exposure, performance, and risk for themselves and their third parties.
Cyber risk ratings and analytics empower organizations to proactively anticipate emerging threats and prioritize risk mitigation efforts based on data-driven insights. Through continuous monitoring of key risk indicators, organizations can gain real-time visibility into a company’s cybersecurity practices and make informed decisions to preemptively manage cyber risk, thereby reducing business risk.
By integrating cyber risk ratings into the onboarding process, organizations can independently assess the cybersecurity performance of third-party vendors and suppliers, including the likelihood of cybersecurity incidents such as data breaches and ransomware events. In turn, this information can inform follow-up due diligence, third-party cybersecurity service-level requirements, and internal risk mitigation actions to minimize the risk of operational disruption as the result of a cybersecurity incident.
In addition to leveraging cyber risk analytics as an early warning signal, the data can also be deployed as a low-latency proxy for broader corporate governance and technology management. Cybersecurity maturity can be seen as a unique proxy for corporate governance and a positive indicator of effective systems and risk management. Organizations that make strategic investments in people, systems, and internal procedures to effectively manage cybersecurity are likely to be more capable of effective business management overall.
Embracing exponential risk with integrated solutions
As cyber threats continue to evolve in sophistication and scale, the imperative for organizations to adopt an integrated approach to risk management is pressing.
Historically, organizations studied and managed risks in silos, defined by the risk area in question or the expertise it required. The supply chain team managed risks within the supply chain. The office of the CIO managed cyber risk.
As new risks emerged, companies assessed data and analyzed them to understand those risks. They added in-house expertise to manage the risks, but they remained siloed, dealt with largely alone.
Now, as leaders witness or experience the impact of exponential risk, they are breaking down internal silos that can limit the ability to see, understand, and address threats. Cross-risk threat analysis and mitigation are now best practice. The focus is less on the individual risk and more on potential combinations.
With the proliferation of data and analytics, compliance teams have an unprecedented opportunity to leverage this insight and gain a comprehensive view of their customers, vendors, suppliers, and counterparties. By harnessing advanced analytics and predictive modeling, organizations can identify patterns and trends indicative of cyber risk and develop targeted strategies to mitigate vulnerabilities proactively.
To help our customers better understand these risk, Moody’s incorporated Bitsight cyber risk ratings and analytics into its compliance and third-party risk workflow automation platform. This allows for the assessment and monitoring of customer and third-party cybersecurity risk during onboarding and due diligence processes.
By adopting a comprehensive approach that addresses both technical and human aspects of cybersecurity, financial institutions and other organizations can effectively mitigate cyber risk among the other key areas of risk being assessed at the same time.
Get in touch
For more information on how to manage and mitigate cyber risk during onboarding and due diligence, please get in touch with the Moody’s team any time.